Avoiding Vendor Lock-In While Optimizing Multi-Cloud Costs
Avoiding vendor lock-in cost optimization guide for 2026. Use Kubernetes, Terraform, and open standards to stay portable while cutting multi-cloud spend.
TLDR;
- Vendor lock-in inflates multi-cloud costs by 20–30% through proprietary APIs, egress fees, and retraining overhead.
- Standardize on Kubernetes, Terraform, and open data formats (Parquet, PostgreSQL) for portability.
- Use abstraction layers like Crossplane and service meshes to isolate cloud-specific code.
- Plan exit strategies from day one with documented data portability and tested failover runbooks.
- EU teams benefit from portability when meeting GDPR and EU Data Act requirements.
Cloud portability is no longer a luxury for European startups and mid-market CTOs watching budgets tighten. Avoiding vendor lock-in cost optimization means architecting workloads so you can move between AWS, Azure, GCP, OVHcloud, or Scaleway without rewriting half your stack.
| Metric | Percentage |
|---|---|
| Enterprises already running multi-cloud | 89% |
| Enterprises confident their data is portable | 32% |
Source: Flexera 2024 State of the Cloud Report
That gap directly translates into higher renewal costs, limited negotiating leverage, and stalled migrations when a cheaper region or provider appears. This cluster covers the open-standard primitives, abstraction patterns, and governance routines that let EU teams keep pricing leverage without sacrificing developer velocity. It pairs with our multi-cloud cost optimization pillar and the cluster on comparing AWS, Azure, and GCP pricing models.
The True Cost of Lock-In
Lock-in shows up in three budget lines:
| Lock-In Source | Cost Impact | Example |
|---|---|---|
| Proprietary services | Premium per-request fees once throughput grows | DynamoDB, Cosmos DB, BigQuery |
| Egress fees | Punishes any migration attempt | $0.09/GB from Frankfurt to internet (after first 100 GB) → 100 TB exit = ~$9,000 |
| Specialized staffing | Salary premiums for provider-specific skills | Each provider requires specialized knowledge |
Source: AWS EC2 on-demand pricing page
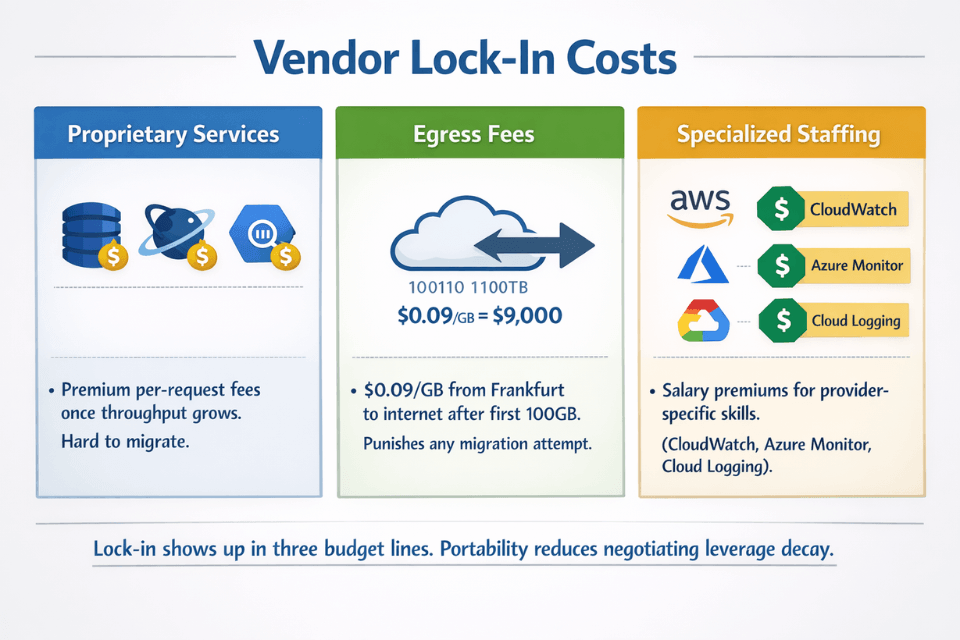
The FinOps Foundation 2024 State of FinOps report lists managing commitment risk across providers as a top practitioner concern, reinforcing that portability and cost discipline travel together.
Open-Standard Building Blocks
Portable architecture starts with shared primitives that behave the same on every cloud.
- Containers and Kubernetes for compute. A conformant cluster on EKS, AKS, GKE, OVHcloud Managed Kubernetes, or Scaleway Kapsule runs the same Helm chart.
- Terraform or OpenTofu for infrastructure. According to the HashiCorp Terraform registry, 4,000+ providers exist, letting one codebase target several clouds.
- PostgreSQL, Kafka, Redis, and ClickHouse for stateful services, available as managed offerings on every major EU provider.
- Open data formats (Parquet, Iceberg, Delta) for analytics, so leaving BigQuery or Redshift does not require reformatting petabytes.
- OpenTelemetry for observability, freeing teams from proprietary agents tied to a single APM vendor.
A Crossplane composition can hide provider-specific resource types behind a common API so developers ask for a PostgresCluster without knowing whether it resolves to RDS or Azure Database for PostgreSQL.
# terraform/modules/object-store/main.tf
variable "provider_name" { type = string }
variable "bucket" { type = string }
resource "aws_s3_bucket" "this" {
count = var.provider_name == "aws" ? 1 : 0
bucket = var.bucket
}
resource "azurerm_storage_account" "this" {
count = var.provider_name == "azure" ? 1 : 0
name = var.bucket
resource_group_name = "rg-eu-west"
location = "westeurope"
account_tier = "Standard"
account_replication_type = "LRS"
}
resource "google_storage_bucket" "this" {
count = var.provider_name == "gcp" ? 1 : 0
name = var.bucket
location = "EUROPE-WEST3"
}
Wrapping storage behind a single module lets finance teams reprice the workload weekly and redeploy to whichever region wins. The same pattern works for managed databases, queues, and load balancers.
Keep a small catalogue of five or six internal modules that map common service needs (object store, relational database, cache, queue, secrets vault, load balancer) to provider-specific resources. Application teams never touch provider APIs directly, and the platform team can swap a backend in a single pull request.
Combined with a Terraform remote state split by cloud, this design supports canary migrations where 10% of traffic runs on a new provider while the original remains authoritative.
Kubernetes + Terraform + open data = portable stack. We build the abstraction layer.
Containers handle compute. Terraform modules hide provider APIs. Parquet and Iceberg keep data portable. OpenTelemetry frees observability.
Our cloud cost optimization experts help you:
- Build provider-agnostic Terraform modules – One codebase deploys to AWS, Azure, GCP, OVHcloud
- Implement Crossplane compositions – Developer asks for
PostgresCluster, platform picks RDS vs. Azure Database - Choose open data formats – Parquet, Iceberg, Delta for analytics portability
- Set up OpenTelemetry – No vendor lock-in for logs, metrics, traces
Optimization Best Practices
Portability does not have to raise costs if you enforce a few disciplines.Portability best practices:
| Strategy | Target | Purpose |
|---|---|---|
| Workloads on open primitives | At least 70% | Reserve proprietary services for differentiating features |
| Committed-use discounts | Bottom 60% of steady-state demand | Stable baseline |
| Spot/preemptible capacity | Top 40% of demand | Any provider can supply (60-91% below on-demand) |
According to the Google Cloud Spot VM documentation, spot prices reach 60–91% below on-demand, matching AWS Spot and Azure Spot VMs closely enough that a portable scheduler like Karpenter or Spot.io can arbitrage across clouds.
| Provider | Discount Range |
|---|---|
| AWS Spot | 60-90% below on-demand |
| Azure Spot | Similar to AWS |
| Google Cloud Spot | 60-91% below on-demand |
Use per-region cost tagging through Terraform so every resource carries team, environment, and sovereignty labels. EU-regulated workloads should pin to Frankfurt, Paris, or Dublin with backup pipelines to a secondary EU provider, satisfying GDPR Article 44 transfer rules and readying the organization for the EU Data Act's portability mandate.
Contract clauses should include data-export SLAs and cap egress fees when a customer chooses to leave, turning portability from a technical property into a commercial one. For deeper tooling reviews, see our cluster on multi-cloud cost management tools.
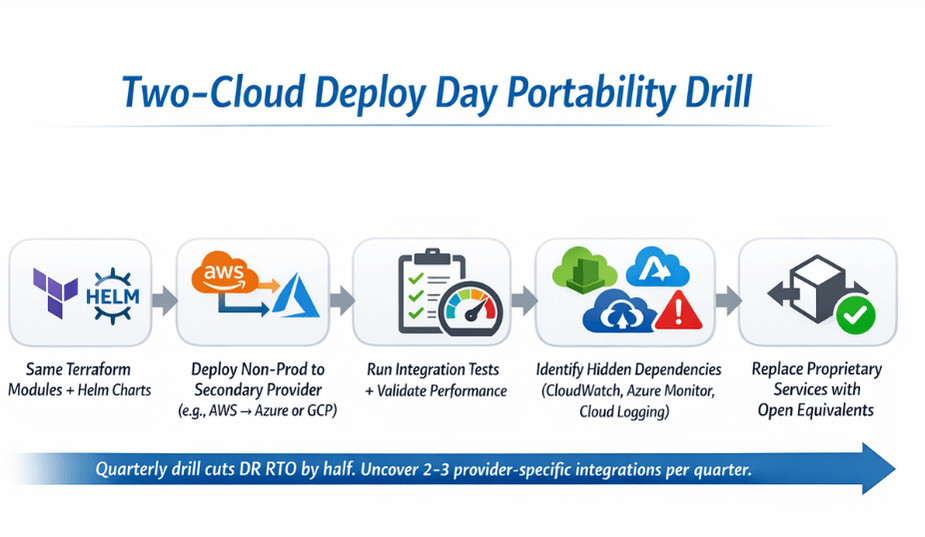
Another practical habit is a "two-cloud deploy day" once per quarter. Quarterly "two-cloud deploy day" benefits:
- Redeploy non-production environment on secondary provider from scratch using same Terraform modules + Helm charts
- Reveals hidden dependencies on provider-specific services (CloudWatch, Cloud Logging, Azure Monitor)
- Teams that run this exercise regularly:
- Cut disaster-recovery RTO by half
- Uncover 2-3 provider-specific integrations per quarter that can be replaced with open equivalents
Monitoring and Governance
Governance keeps the portable design from drifting back toward lock-in.
| Practice | Frequency | Purpose |
|---|---|---|
| Architecture reviews | Quarterly | Flag new single-cloud-only services |
| Portability KPI tracking | Quarterly | Target 75%+ compute on Kubernetes |
| Exit-readiness drill | Every 6 months | Restore production data into second cloud from object-storage snapshots |
| Unit economics monitoring | Continuous | Kubecost/OpenCost per-namespace costs across clusters |
For workload placement patterns, review our cluster on multi-cloud workload distribution strategies and related work on Kubernetes cost optimization techniques.
Conclusion
Avoiding vendor lock-in cost optimization is a strategic advantage, not a technical obsession. EU CTOs who ground their stack in Kubernetes, Terraform, open data formats, and observable governance keep negotiating power during every renewal and stay ready for regulatory shifts like the EU Data Act.
The payoff is measurable: a 15–25% drop in cloud spend over three years and a cleaner path to adding regional providers when data sovereignty rules tighten. If you need help benchmarking your current architecture or building a portable reference stack, EaseCloud's multi-cloud advisory team can run a two-week readiness assessment with your engineering leads.
Frequently Asked Questions
Does multi-cloud always cost more than single-cloud?
Not if you use shared primitives.
| Factor | Financial Impact |
|---|---|
| Duplicated control planes overhead | +5-10% |
| Negotiating leverage + spot arbitrage recovery | -15-25% |
| Net multi-cloud cost vs. single-cloud | Not necessarily higher (if using shared primitives) |
Is Kubernetes enough to avoid lock-in?
Open Stack Components for Portability
- Kubernetes – handles compute portability (but not data)
- Open databases – data portability
- Object-storage abstractions – storage portability
- Infrastructure as Code (Terraform) – deployment portability
Keys to true portability: Kubernetes + open databases + object-storage abstractions + IaC layer
How do EU startups stay compliant while staying portable?
EU Compliance + Portability Requirements:
- Pin regulated data to EU regions (Frankfurt, Paris, Dublin)
- Tag every resource with a sovereignty label
- Contract with providers offering GDPR-aligned data processing addenda (OVHcloud, Scaleway)
- Backup pipelines to a secondary EU provider
- Satisfies GDPR Article 44 transfer rules
- Ready for EU Data Act portability mandate
Summarize this post with:
Ready to put this into production?
Our engineers have deployed these architectures across 100+ client engagements — from AWS migrations to Kubernetes clusters to AI infrastructure. We turn complex cloud challenges into measurable outcomes.