CI/CD Pipeline Security and Compliance Best Practices
Secure your CI/CD pipelines with secret scanning, container image verification, SBOM generation, and SLSA compliance. Protect against supply chain attacks in 2026.

TLDR;
- Supply chain attacks increased 742% since 2019, making pipeline security a top priority
- Shift-left security catches 85% of vulnerabilities before code reaches production
- Container signing, SBOM generation, and policy-as-code automate compliance checks
- European organizations must align pipeline controls with GDPR audit trail requirements
Your CI/CD pipeline is the gateway between source code and production. Every artifact, secret, and configuration flows through it. That makes pipelines a high-value target for attackers. According to Sonatype's State of the Software Supply Chain 2024, supply chain attacks on open-source projects have grown 742% since 2019, with attackers increasingly targeting build systems and dependency chains.
The good news: mature tooling exists to secure every stage of your pipeline. Pre-commit hooks catch secrets before they enter version control. Automated scanners flag vulnerable dependencies during builds. Container signing proves artifact integrity at deployment time. Policy engines reject non-compliant workloads before they run.
This article covers practical security controls you can implement across your pipeline today. For European B2B organizations, pipeline security also serves compliance requirements.
GDPR compliance requirements:
- Demonstrable data protection measures
- Audit trails through CI/CD processes provide evidence of secure software delivery
- Choose secret management systems that support EU data residency
Shift-Left Security Controls
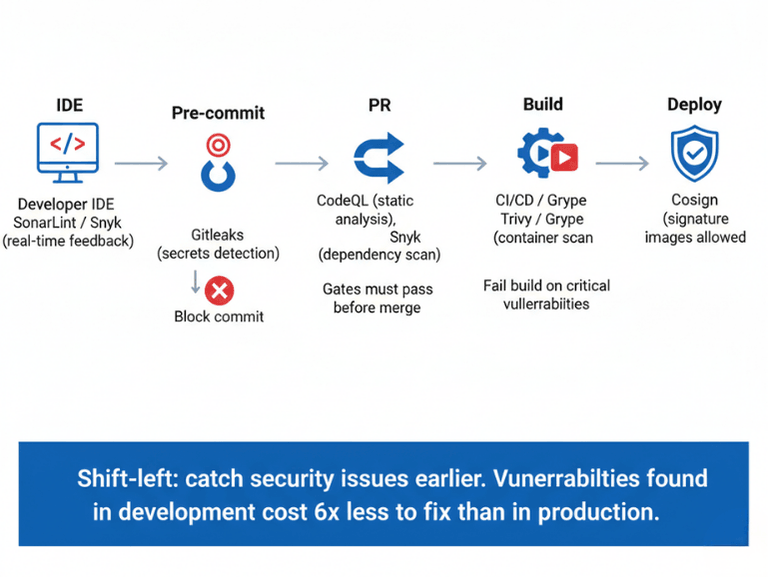
[Developer IDE] --> [Pre-commit Hooks] --> [PR Checks] --> [Build Scan] --> [Deploy Verify]
| | | | |
[SonarLint] [Gitleaks] [CodeQL] [Trivy] [Cosign]
Catching security issues early is cheaper and faster than finding them in production. According to IBM's Cost of a Data Breach Report 2024, vulnerabilities found during development cost 6x less to remediate than those discovered in production.
Pre-commit hooks prevent secrets from entering version control:
#!/bin/bash
# .git/hooks/pre-commit
if gitleaks protect --staged; then
echo "No secrets detected"
else
echo "Secrets detected - commit blocked"
exit 1
fi
Pull request checks run static analysis and dependency scanning before merge:
name: Security Checks
on: pull_request
jobs:
security:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Secret scanning
uses: gitleaks/gitleaks-action@v2
- name: Dependency scanning
run: snyk test --severity-threshold=high
- name: Static analysis
uses: github/codeql-action/analyze@v2
These gates must pass before merge, preventing security issues from reaching the main branch. IDE extensions like Snyk and SonarLint provide real-time feedback during development without breaking developer flow.
Dependency and Container Scanning
Your application depends on hundreds of third-party packages. Each one is a potential vulnerability vector. According to Snyk's State of Open Source Security 2024, the average application contains 49 vulnerabilities across its dependency tree.
Pin exact dependency versions for reproducible builds:
{
"dependencies": {
"express": "4.18.2"
}
}
Lock files (package-lock.json, yarn.lock, Pipfile.lock) are mandatory. Use Dependabot or Renovate to create PRs for intentional updates.
Scan container images during builds:
build:
script:
- docker build -t myapp:${CI_COMMIT_SHA} .
- trivy image myapp:${CI_COMMIT_SHA} --severity HIGH,CRITICAL --exit-code 1
Use minimal base images to reduce attack surface. Distroless images contain only your application and runtime dependencies with no shell, no package manager, and no utilities an attacker could exploit.
FROM golang:1.21 AS builder
WORKDIR /app
COPY . .
RUN go build -o server
FROM gcr.io/distroless/static-debian11
COPY --from=builder /app/server /
USER nonroot:nonroot
ENTRYPOINT ["/server"]
49 vulnerabilities per application on average. We help you find and fix them.
Third-party dependencies are the #1 source of vulnerabilities. Scanning them requires tooling and processes.
We help you:
- Automate dependency scanning – Trivy, Grype, Snyk in CI pipelines
- Pin exact versions – Lock files, Dependabot for intentional updates
- Scan container images – Fail builds on HIGH/CRITICAL vulnerabilities
- Use minimal base images – Distroless, Alpine to reduce attack surface
Artifact Signing and Verification
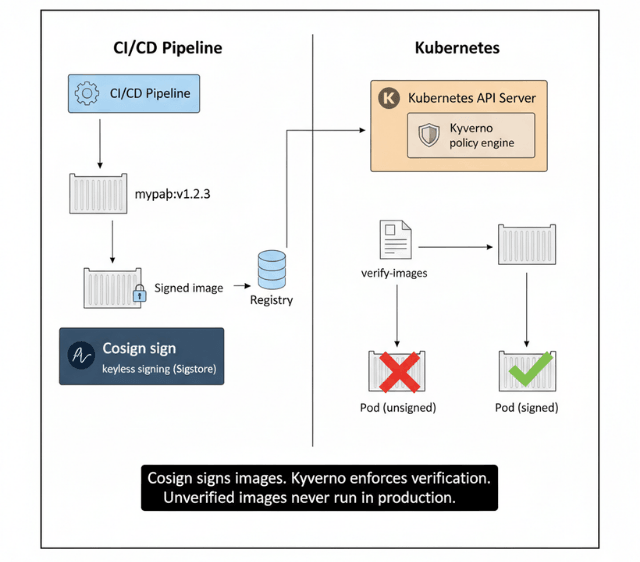
Cryptographic signing proves an artifact was built by your trusted pipeline and has not been tampered with. Sigstore Cosign provides keyless signing backed by certificate transparency logs.
cosign sign --yes registry.example.com/myapp:v1.2.3
cosign verify registry.example.com/myapp:v1.2.3
Enforce verification at deployment with Kyverno:
apiVersion: kyverno.io/v1
kind: ClusterPolicy
metadata:
name: verify-images
spec:
validationFailureAction: enforce
rules:
- name: verify-signature
match:
resources:
kinds:
- Pod
verifyImages:
- imageReferences:
- "registry.example.com/*"
attestors:
- entries:
- keyless:
issuer: https://token.actions.githubusercontent.com
This policy prevents unsigned or unverified images from running in your cluster. Combined with artifact management practices, signing creates an unbroken chain of trust from source to production.
Secret Management
Secrets in pipelines are a major security risk. Never store them in source code or directly in environment variables where they appear in logs and process listings.
Use dedicated secret management systems:
- HashiCorp Vault
- AWS Secrets Manager
- Azure Key Vault
- Google Secret Manager
For European organizations: Choose systems that support EU data residency to maintain GDPR compliance.
Short-lived credentials eliminate credential rotation burden:
jobs:
deploy:
runs-on: ubuntu-latest
permissions:
id-token: write
contents: read
steps:
- name: Configure AWS credentials
uses: aws-actions/configure-aws-credentials@v4
with:
role-to-assume: arn:aws:iam::123456789012:role/GitHubActions
aws-region: eu-west-1
OIDC federation with cloud providers means no long-lived credentials stored anywhere. Each pipeline run receives temporary credentials that expire after the job completes.
Kubernetes External Secrets Operator syncs secrets from external systems into cluster secrets without committing sensitive values to Git.
Policy as Code and Compliance
Replace manual security reviews with automated policy enforcement. Open Policy Agent (OPA) and Kyverno evaluate every deployment against defined rules.
apiVersion: kyverno.io/v1
kind: ClusterPolicy
metadata:
name: require-non-root
spec:
validationFailureAction: enforce
rules:
- name: check-runAsNonRoot
match:
resources:
kinds:
- Pod
validate:
message: "Containers must run as non-root"
pattern:
spec:
containers:
- securityContext:
runAsNonRoot: true
Generate Software Bill of Materials (SBOM) for every artifact:
syft packages registry.example.com/myapp:v1.2.3 -o spdx-json > sbom.json
SBOMs provide instant answers to "are we affected?" when new vulnerabilities are announced. According to the SLSA framework, most organizations should target Level 2-3 for production pipelines, which requires tamper-proof build services with automatically generated provenance.
For European B2B compliance the audit requirements are:
- Maintain immutable audit logs of all pipeline activities:
- Who triggered builds
- What artifacts were produced
- Who approved deployments
- Satisfies GDPR accountability principle
- Supports regulatory audits under PSD2 and MiFID II
Conclusion
Pipeline security in 2026 demands a layered approach. Start with shift-left controls: pre-commit hooks for secret scanning, PR gates for dependency and static analysis. Add container image scanning and signing during build processes. Enforce policies at deployment time with OPA or Kyverno.
Short-lived credentials, SBOM generation, and SLSA compliance round out a mature pipeline security posture. Integrate these controls into your GitOps workflow and progressive delivery process to maintain security without slowing CI/CD pipeline velocity.
FAQs
What is SLSA and why does it matter for CI/CD pipelines?
SLSA (Supply-chain Levels for Software Artifacts) is a security framework that provides a maturity model for build systems.
| Level | Requirements | Target |
|---|---|---|
| Level 1 | Documented build process | Starting point |
| Level 2 | Tamper-proof build service | Most organizations target Level 2-3 |
| Level 3 | Automatic provenance generation | Most organizations target Level 2-3 |
| Level 4 | Hermetic, reproducible builds | Highest maturity |
How do I prevent secrets from leaking in CI/CD pipelines?
Use three controls:
| Control | Tool/Method | Purpose |
|---|---|---|
| Pre-commit hooks | Gitleaks, TruffleHog | Catch secrets before they enter Git |
| Dedicated secret management | Vault, AWS Secrets Manager | Secure storage |
| OIDC federation | Short-lived credentials | Credentials that never need rotation |
What container scanning tools should I use?
Trivy and Grype are popular open-source options. Run them during builds with --exit-code 1 to fail builds on high-severity vulnerabilities. Combine with registry-level scanning (AWS ECR, Azure ACR) for continuous monitoring of deployed images.
Summarize this post with:
Ready to put this into production?
Our engineers have deployed these architectures across 100+ client engagements — from AWS migrations to Kubernetes clusters to AI infrastructure. We turn complex cloud challenges into measurable outcomes.