Balancing Security and Performance in SaaS Applications
Balance strong security with high performance in SaaS apps using optimized encryption, JWT caching, input validation, database policies, and edge-level protections.

Security and performance often seem at odds. Encryption adds CPU overhead. Authentication checks add latency. Input validation consumes processing time. Yet both are non-negotiable for SaaS applications. The goal isn't choosing between security and performance but implementing security efficiently. Modern techniques and proper architecture enable strong security with minimal performance impact.
The Security-Performance Tradeoff
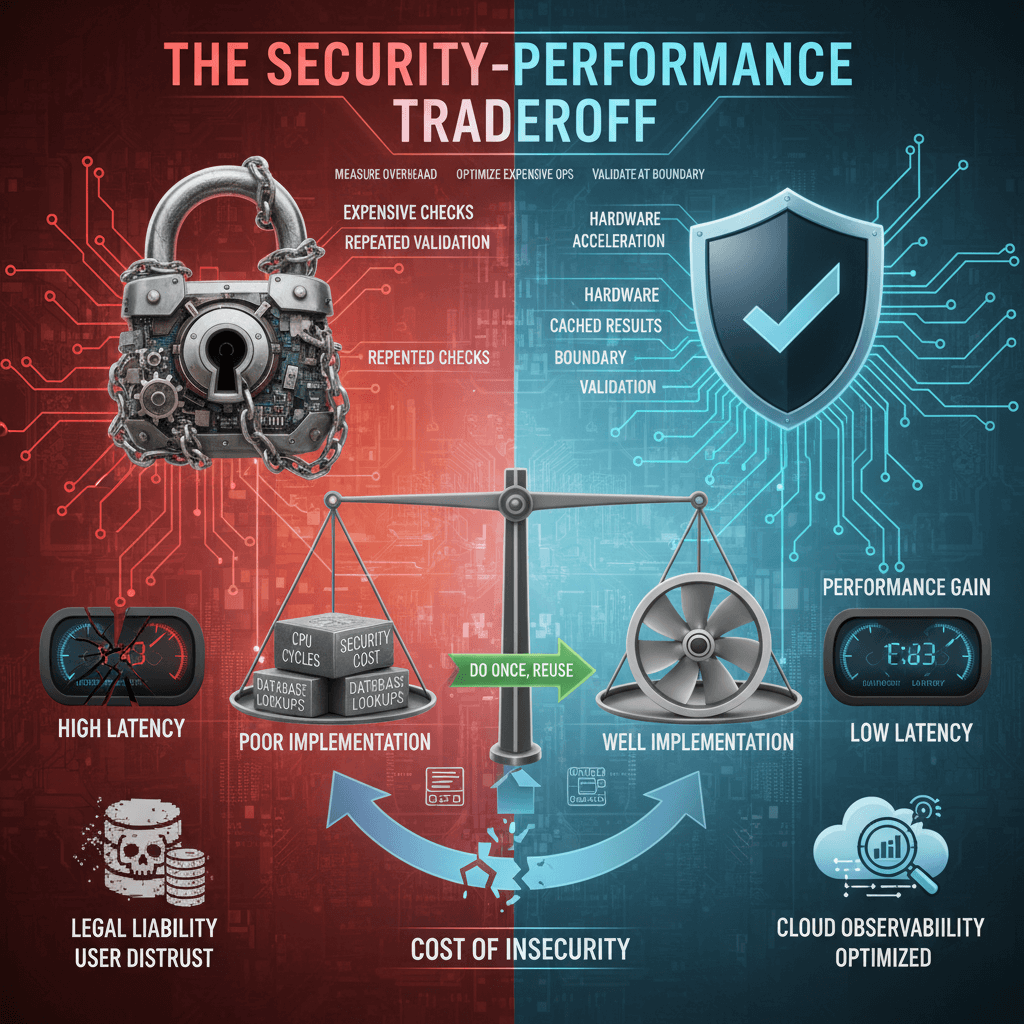
Every security measure has a cost. Encryption requires CPU cycles. Token validation requires database or cache lookups. Security logging consumes I/O bandwidth. These costs compound across thousands of requests.
Poorly implemented security creates significant overhead. Validating the same token repeatedly, encrypting already-encrypted data, or running expensive checks on every request can dominate response time.
Well-implemented security adds minimal overhead. Caching authentication results, using hardware-accelerated encryption, and validating at appropriate boundaries keep security costs low.
The key principle is doing security work once and reusing results. Validate a JWT once per request, not once per function call. Cache authorization decisions for the session. Verify input at the boundary, not in every layer.
Measure security overhead explicitly. Profile authentication, encryption, and validation separately. Profile authentication, encryption, and validation separately, and use a cloud observability strategy to correlate security and performance metrics. Identify which security operations consume the most time. Optimize the expensive ones first.
Security failures have performance costs too. Data breaches damage user trust and create legal liability. DDoS attacks cause complete outages. The "cost" of security must include the cost of not having it.
Encryption Performance
TLS encryption protects data in transit. Modern TLS with hardware acceleration adds negligible overhead. Older protocols and configurations add unnecessary cost.
TLS 1.3 reduces handshake latency. Fewer round trips establish connections faster. Enable TLS 1.3 and disable older protocols when possible.
# Nginx TLS configuration
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256;
ssl_prefer_server_ciphers off;
ssl_session_cache shared:SSL:10m;
ssl_session_timeout 1d;
ssl_session_tickets off;
Session resumption avoids full handshakes on reconnection. TLS session caching and session tickets reduce overhead for returning clients.
ECDSA certificates provide equivalent security with smaller key sizes than RSA. Smaller keys mean faster cryptographic operations.
AES-GCM cipher suites leverage hardware acceleration. Modern CPUs include AES-NI instructions that encrypt data with minimal overhead. Avoid CBC mode ciphers when possible.
Application-layer encryption adds its own overhead. Encrypt only what needs encryption. Field-level encryption protects sensitive data without encrypting everything.
from cryptography.fernet import Fernet
# Encrypt only sensitive fields, not entire records
def store_user(user_data):
user_data['ssn'] = encrypt_field(user_data['ssn'])
user_data['credit_card'] = encrypt_field(user_data['credit_card'])
# name, email, etc. stored unencrypted
db.users.insert(user_data)
Key management affects encryption performance. Local key caching avoids network calls to key management services on every operation.
Authentication Optimization
JWT validation can happen locally without database calls. Once issued, JWTs contain all necessary claims. Verify the signature and check expiration locally.
const jwt = require('jsonwebtoken');
function validateToken(token) {
// No database call needed
return jwt.verify(token, PUBLIC_KEY, { algorithms: ['RS256'] });
}
Token caching reduces validation overhead for session-based auth. After the first validation, cache the result keyed by token. Check the cache before running full validation.
Short-lived access tokens with refresh tokens balance security and performance. Access tokens (15-60 minutes) validate locally. Refresh tokens require database checks but run infrequently.
Session validation should happen once per request at the gateway. Don't repeat authentication checks in every microservice. Pass validated user context between services.
# Gateway validates once
@app.before_request
def authenticate():
token = request.headers.get('Authorization')
request.user = validate_and_cache_token(token)
# Downstream handlers use validated context
@app.route('/api/orders')
def get_orders():
return Order.query.filter_by(user_id=request.user['id']).all()
Password hashing uses intentionally slow algorithms (bcrypt, Argon2). This happens at login, not on every request. The overhead is acceptable for login operations.
OAuth token introspection adds network latency. Cache introspection results with appropriate TTLs. Balance freshness requirements against performance needs.
Input Validation Efficiency
Validate input at system boundaries. Check request data when it enters your system. Validated data doesn't need rechecking in downstream functions.
Schema validation libraries provide efficient checking. JSON Schema, Joi, and similar libraries validate efficiently. Compile schemas once and reuse validators.
const Ajv = require('ajv');
const ajv = new Ajv();
// Compile once at startup
const validateOrder = ajv.compile({
type: 'object',
required: ['items', 'customerId'],
properties: {
items: { type: 'array', minItems: 1 },
customerId: { type: 'string', format: 'uuid' }
}
});
// Validate on each request
function createOrder(req, res) {
if (!validateOrder(req.body)) {
return res.status(400).json(validateOrder.errors);
}
// Proceed with validated data
}
Fail fast on invalid input. Reject malformed requests before doing any work. Don't query databases or call services with invalid data.
Size limits prevent resource exhaustion. Limit request body size, file upload size, and array lengths. Large payloads consume memory and processing time.
Content-Type checking prevents unexpected processing. Reject requests with incorrect Content-Type headers before parsing.
Regex validation can be expensive. Complex regular expressions with backtracking can be exploited for ReDoS attacks. Use simple patterns or specialized validators.
// Avoid: catastrophic backtracking possible
const badRegex = /^(a+)+$/;
// Prefer: linear-time alternatives
const emailValidator = require('email-validator');
if (!emailValidator.validate(email)) {
return false;
}
Database Security Without Slowdown
Parameterized queries prevent SQL injection without performance penalty. Query planners optimize parameterized queries the same as string-built queries.
# Secure and equally performant
cursor.execute(
"SELECT * FROM users WHERE email = %s AND status = %s",
(email, 'active')
)
Row-level security (RLS) enforces access at the database level. PostgreSQL's RLS applies policies automatically. This moves security checks to the database, often faster than application-level filtering.
-- Enable row-level security
ALTER TABLE orders ENABLE ROW LEVEL SECURITY;
CREATE POLICY tenant_isolation ON orders
USING (tenant_id = current_setting('app.tenant_id')::uuid);
Connection user privileges limit blast radius. Application database users should have minimal necessary permissions. Read-only replicas use read-only database users.
Encryption at rest is handled by the database or storage layer. Modern databases encrypt transparently with hardware acceleration. Application code doesn't see the overhead.
Audit logging can impact performance significantly. Log security-relevant events, not every query. Use async logging to avoid blocking request processing.
Rate Limiting and DDoS Protection
Rate limiting protects against abuse while minimizing legitimate user impact. Implement limits that trigger only on abnormal behavior.
Sliding window algorithms provide smoother limiting than fixed windows. They prevent request bursts at window boundaries.
import redis
import time
def is_rate_limited(user_id, limit=100, window=60):
r = redis.Redis()
now = time.time()
key = f"rate:{user_id}"
pipe = r.pipeline()
pipe.zremrangebyscore(key, 0, now - window)
pipe.zadd(key, {str(now): now})
pipe.zcard(key)
pipe.expire(key, window)
results = pipe.execute()
return results[2] > limit
Edge-level rate limiting handles traffic before it reaches application servers. CDNs and load balancers can enforce limits with minimal latency impact.
Different limits for different endpoints make sense. Login endpoints need stricter limits than read operations. Resource-intensive operations need lower limits.
Bot detection distinguishes legitimate traffic from attacks. CAPTCHAs and behavioral analysis identify suspicious clients. Only challenge suspicious traffic, not everyone.
DDoS protection services absorb attack traffic. Cloudflare, AWS Shield, and similar services handle volumetric attacks at the edge. Application servers never see attack traffic.
Security Headers and HTTPS
Security headers protect without significant overhead. Headers like Content-Security-Policy, X-Content-Type-Options, and Strict-Transport-Security are bytes in the response.
# Security headers in Nginx
add_header Strict-Transport-Security "max-age=31536000; includeSubDomains" always;
add_header X-Content-Type-Options "nosniff" always;
add_header X-Frame-Options "DENY" always;
add_header Content-Security-Policy "default-src 'self'" always;
HSTS eliminates HTTP-to-HTTPS redirects, and current TLS best practices (e.g., using TLS 1.3 and strong ciphers) strongly recommend disabling legacy protocols to balance security and performance.. Browsers remember HTTPS requirement, removing redirect latency. Preloading HSTS provides this benefit from the first visit.
Content-Security-Policy can improve performance by blocking unwanted resources. Inline script restrictions reduce attack surface and can trigger browser optimizations.
CORS configuration happens once per preflight. Browsers cache CORS preflight responses. Set appropriate Access-Control-Max-Age to reduce preflight frequency.
Access-Control-Max-Age: 86400
Cookie security attributes (Secure, HttpOnly, SameSite) add no overhead. These are parsed once when setting cookies.