Managing Cloud-Native Infrastructure as Code
Master cloud-native Infrastructure as Code with Terraform, Pulumi, GitOps, and Kubernetes. Build scalable, secure, and fully automated platforms.
Introduction
Cloud native infrastructure as code revolutionizes infrastructure management by defining resources through declarative code rather than manual configuration. This approach enables automated, repeatable deployments across Kubernetes clusters, cloud providers, and distributed environments. Platform engineers and DevOps teams leverage IaC to achieve unprecedented velocity while maintaining security and compliance through version-controlled infrastructure definitions and modern platform engineering practices.
What is Cloud-Native Infrastructure as Code
Cloud native IaC converges Infrastructure as Code with cloud native computing, managing containerized applications, Kubernetes resources, and cloud infrastructure through declarative configurations. Unlike traditional IaC provisioning static servers, cloud native IaC addresses dynamic requirements of microservices, container orchestration, and ephemeral infrastructure.
The key distinction lies in managing not just compute and networking, but Kubernetes clusters, namespaces, service meshes, ingress controllers, and platform services. Everything from cloud provider resources to Kubernetes manifests exists as version-controlled code, enabling complete environment recreation from repositories.
Cloud native IaC emphasizes declarative configuration, immutability, and GitOps workflows. Teams declare desired infrastructure state, and automated systems continuously reconcile actual state. This approach aligns with cloud native principles where applications are ephemeral, infrastructure is cattle not pets, and everything can be recreated from code.
For platform engineers, this means provisioning complete environments in minutes, replicating production for testing, and recovering from disasters by reapplying infrastructure code. Infrastructure provisioning ties to application commits, automatically scaling and updating to support application requirements.
The GitOps Operating Model
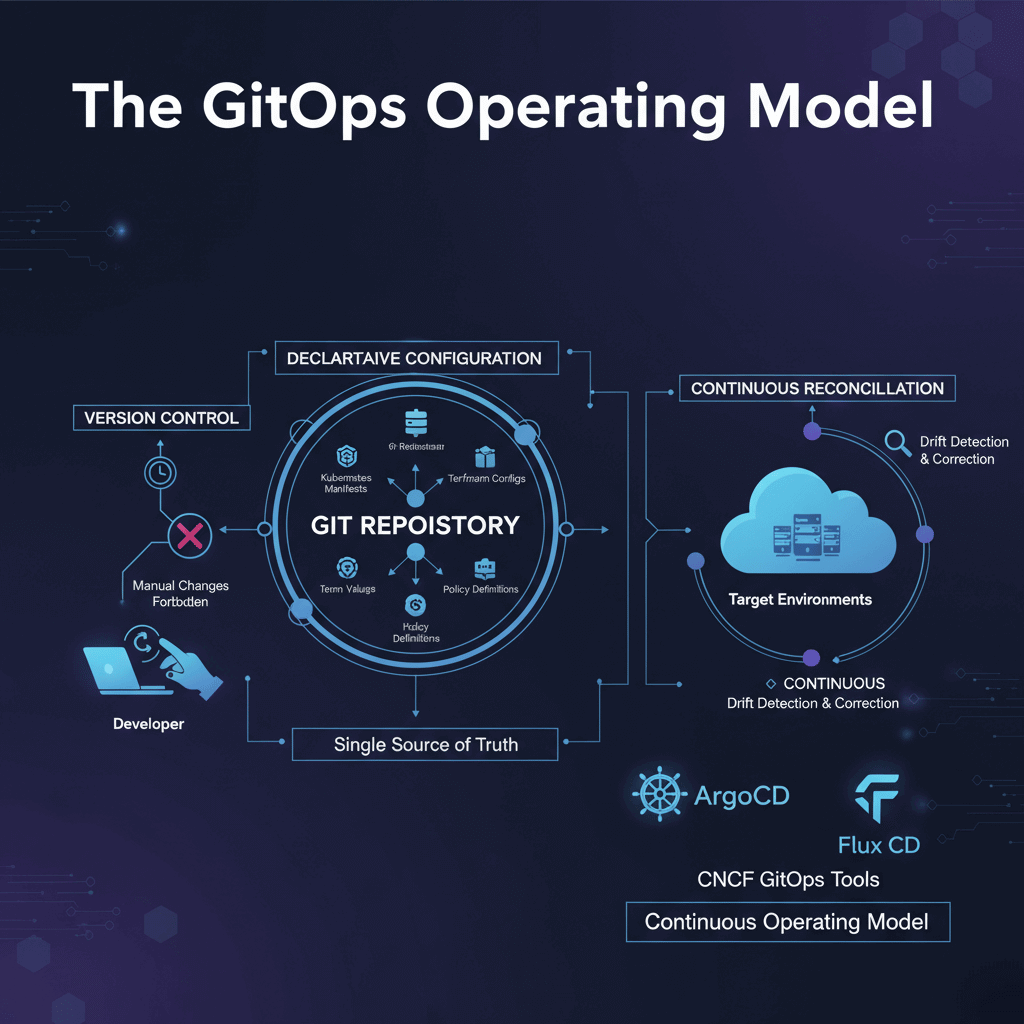
GitOps establishes Git as the single source of truth for infrastructure and applications. The methodology builds on declarative configuration, version control, automated synchronization, and continuous reconciliation.
Declarative configuration describes entire desired state in Git repositories, including Kubernetes manifests, Terraform configurations, Helm values, and policy definitions. This enables automated systems to understand target state without procedural instructions.
Version control as source makes Git the authority for what should run in environments. All changes must be committed to Git. Manual changes to running systems are forbidden or automatically reverted by reconciliation loops. This discipline ensures complete auditability and reproducibility.
Automated synchronization continuously monitors Git repositories and automatically synchronizes changes to target environments. When developers merge pull requests modifying infrastructure code, automated agents detect changes and apply them to clusters.
Continuous reconciliation continuously monitors infrastructure and compares against declared state in Git. If drift occurs through manual changes, failures, or attacks, the system automatically corrects it, bringing environments back into compliance.
GitOps tools like ArgoCD and Flux CD dominate the Kubernetes environment, following principles outlined by the Cloud Native Computing Foundation (CNCF). ArgoCD provides visual web UI showing cluster state, application health, and synchronization status. Flux CD follows Unix philosophy with composable components for different concerns. Both tools transform infrastructure management from deployment mechanism into continuous operating model.
Essential Tools for Cloud-Native IaC
Terraform has emerged as the de facto standard for cloud-agnostic infrastructure provisioning. Using HashiCorp Configuration Language, Terraform defines resources across hundreds of providers. It excels at provisioning foundational infrastructure including VPCs, compute instances, managed databases, and Kubernetes clusters.
Terraform workflows center on plan and apply operations. Running terraform plan shows exactly what resources will be created, modified, or destroyed before changes. This preview capability prevents mistakes in production. Terraform state files track current infrastructure, enabling drift detection and reconciliation.
Pulumi represents infrastructure as code using general-purpose programming languages like Python, TypeScript, and Go. This enables full IDE support with autocomplete, type checking, loops without DSL limitations, standard library access, and unit testing using familiar frameworks.
Pulumi integrates seamlessly with Kubernetes, provisioning cloud resources, creating clusters, and deploying applications in the same codebase. Strongly-typed resources catch configuration errors at development time rather than deployment.
Helm is the package manager for Kubernetes, functioning like apt or npm for containerized applications. Helm packages called charts bundle Kubernetes manifest templates with metadata and default values. Charts provide standard formats for distributing applications, parameterization without duplication, dependency management, and versioned deployments with rollback capabilities.
The Artifact Hub hosts thousands of community-maintained charts for popular applications. Teams deploy complex applications with single helm install commands rather than applying dozens of individual YAML files.
Crossplane extends Kubernetes with infrastructure provisioning capabilities, allowing platform teams to define and manage cloud resources through Kubernetes-native APIs. Crossplane uses the operator pattern to reconcile desired infrastructure state with actual cloud provider resources, composing into higher-level abstractions matching organizational concepts.
Declarative vs. Imperative Approaches
Imperative infrastructure tells systems how to achieve goals through step-by-step instructions. Scripts contain commands like "create this server, install these packages, start this service." The focus is on procedure, the sequence of actions required.
Imperative approaches offer precise control but have drawbacks. They're fragile as later steps fail if earlier steps didn't complete exactly as expected. They're difficult to manage state, as re-running scripts might create duplicates. They're harder to reason about, requiring understanding entire procedures to predict outcomes.
Declarative infrastructure specifies what the final state should be without prescribing how to achieve it. You declare "I want three application servers with these specifications running this container image" and the IaC tooling determines necessary steps.
Declarative approaches provide significant advantages. They're idempotent, applying the same declaration multiple times produces the same result. They enable automated reconciliation as systems continuously ensure actual state matches declared state. They're more maintainable as engineers only need to understand desired outcomes. They support self-healing when drift occurs, systems know what state to restore.
Cloud native infrastructure strongly favors declarative approaches. Kubernetes itself is fundamentally declarative. You submit resource definitions describing desired state, and controllers continuously work to achieve and maintain that state. Terraform, Pulumi, and GitOps tools all operate on declarative principles.
IaC Best Practices
Version control and Git workflows require every infrastructure definition in version control with no exceptions. Git workflows requiring peer review for infrastructure changes prevent mistakes. Reviewers verify changes align with security policies, don't introduce unnecessary costs, and follow organizational standards.
Use separate repositories or directory structures for different environments. While tempting to use branches for environments, this leads to merge conflicts and drift. Maintain separate codebases parameterized for each environment, ensuring changes flow from development to production through promotion.
Modularization and reusability avoid monolithic configurations. Break infrastructure into focused, reusable modules composable to build complete systems. Terraform modules, Pulumi components, and Helm charts all support this modularity. Well-designed modules encapsulate complexity behind simple interfaces.
Establish module versioning and maintain backward compatibility. Modules should be treated as internal products with semantic versioning. Major version increments signal breaking changes, minor versions add features, patches fix bugs.
Security and secrets management never commit secrets, API keys, passwords, or certificates to version control. Even private repositories shouldn't contain secrets. Instead, integrate dedicated secrets management solutions like HashiCorp Vault, AWS Secrets Manager, Azure Key Vault, and Google Cloud Secret Manager.
Implement policy as code to enforce security standards automatically. Open Policy Agent and HashiCorp Sentinel enable writing policies validating infrastructure configurations before deployment. Policies might prevent public S3 buckets, enforce encryption at rest, require specific network configurations, or validate compliance.
Automated testing and validation treat infrastructure code with same testing rigor as application code. Implement multiple testing layers including syntax validation, unit tests, integration tests, and compliance tests. For Terraform, use terraform validate for syntax, terraform-compliance for policy validation, and Terratest for integration testing.
Kubernetes and Infrastructure as Code
Kubernetes introduces unique IaC considerations, blurring lines between infrastructure and application deployment. The relationship operates at multiple levels.
At the foundation level, IaC tools provision Kubernetes clusters themselves, creating control planes, worker nodes, networking, and cloud provider integrations. Terraform, Pulumi, and cloud-specific tools excel at this cluster provisioning layer.
Within clusters, IaC manages Kubernetes resources including namespaces, deployments, services, ingress rules, and persistent volumes. Tooling options multiply: kubectl with raw YAML, Kustomize for manifest customization, Helm for packaged applications, or custom operators for specialized workloads.
Kubernetes as IaC Platform - Kubernetes itself functions as infrastructure as code. The Kubernetes API accepts declarative resource definitions and continuously reconciles actual state to match declared state. Controllers watch for resource changes and take action to realize them.
State management becomes a critical decision. When using Terraform to manage in-cluster resources, Terraform maintains state about those resources. However, Kubernetes also maintains state internally. This dual state can lead to conflicts, especially when resources are modified outside Terraform.
Many platform engineers adopt layered approaches: use Terraform or Pulumi to provision clusters and cloud resources, but use Kubernetes-native tools like Helm, Kustomize, ArgoCD, and Flux to manage in-cluster resources. This separation leverages each tool's strengths and avoids state conflicts.
Cluster bootstrapping commonly uses Terraform or Pulumi to provision clusters, then deploys GitOps operators like ArgoCD or Flux into the cluster. The GitOps operators then manage all in-cluster resources from Git repositories. This provides cloud-agnostic cluster provisioning while leveraging Kubernetes-native deployment for applications.
Conclusion
Cloud native infrastructure as code fundamentally transforms infrastructure management from manual, error-prone processes into automated, version-controlled workflows. By treating infrastructure with the same rigor as application code, organizations achieve unprecedented velocity, reliability, and scale.
The convergence of IaC tools like Terraform and Pulumi with cloud native platforms like Kubernetes, orchestrated through GitOps methodologies with ArgoCD and Flux, creates powerful platform engineering foundations. This foundation enables self-service developer experiences, automated compliance enforcement, and infrastructure that evolves continuously with application requirements.
Success requires more than adopting tools. It demands cultural transformation toward declarative thinking, automation-first mindsets, and collaborative workflows. Platform teams must establish clear patterns, provide reusable modules, implement guardrails through policy as code, and maintain comprehensive observability.
The challenges are real including managing state complexity, preventing configuration drift, securing secrets, and testing infrastructure thoroughly. But benefits far outweigh implementation effort through consistency across environments, rapid provisioning, complete auditability, and effortless disaster recovery.
As cloud native ecosystems evolve toward AI-driven optimization and sustainability-focused practices, infrastructure as code becomes increasingly intelligent and automated. Platform engineers who master these principles and tools today position their organizations for success in tomorrow's cloud native environment.