Automating Cloud-Native Deployments with CI/CD
Learn how to automate cloud-native deployments with CI/CD, GitOps, and progressive delivery on Kubernetes—secure, scalable, and production-ready.

Introduction
Cloud native CI/CD pipelines automate software delivery from code commit to production deployment, enabling organizations to deploy hundreds of times daily with confidence. Modern pipelines integrate containerization, Kubernetes orchestration, security scanning, and progressive delivery patterns that transform deployment from risky events into routine operations. This guide covers pipeline architecture, GitOps workflows, security integration, and best practices that accelerate delivery while maintaining quality.
Understanding Cloud-Native CI/CD
Cloud native CI/CD differs from traditional pipelines by embracing containers, declarative configuration, and Kubernetes-native tooling. Pipelines build container images instead of deploying to static servers. They use Kubernetes manifests and Helm charts instead of configuration management scripts. They leverage GitOps workflows where Git repositories serve as the single source of truth for both application and infrastructure state.
Continuous Integration automatically builds, tests, and validates every code change. Developers commit code frequently, triggering automated builds that compile code, run unit tests, perform static analysis, scan for security vulnerabilities, and package applications into container images. Fast feedback loops enable developers to catch and fix issues immediately while context is fresh.
Continuous Deployment automates application delivery to production environments following successful CI validation. CD pipelines deploy container images to Kubernetes clusters, execute integration tests in staging environments, gradually roll out changes using progressive delivery techniques, and automatically roll back failures detected through monitoring.
Cloud native pipelines emphasize declarative configuration over imperative scripts. Pipeline definitions exist as code in version control, enabling peer review, versioning, and reproducibility. Tools like Tekton define pipelines as Kubernetes Custom Resources, treating CI/CD infrastructure as native cluster resources.
Kubernetes-Native CI/CD Tools
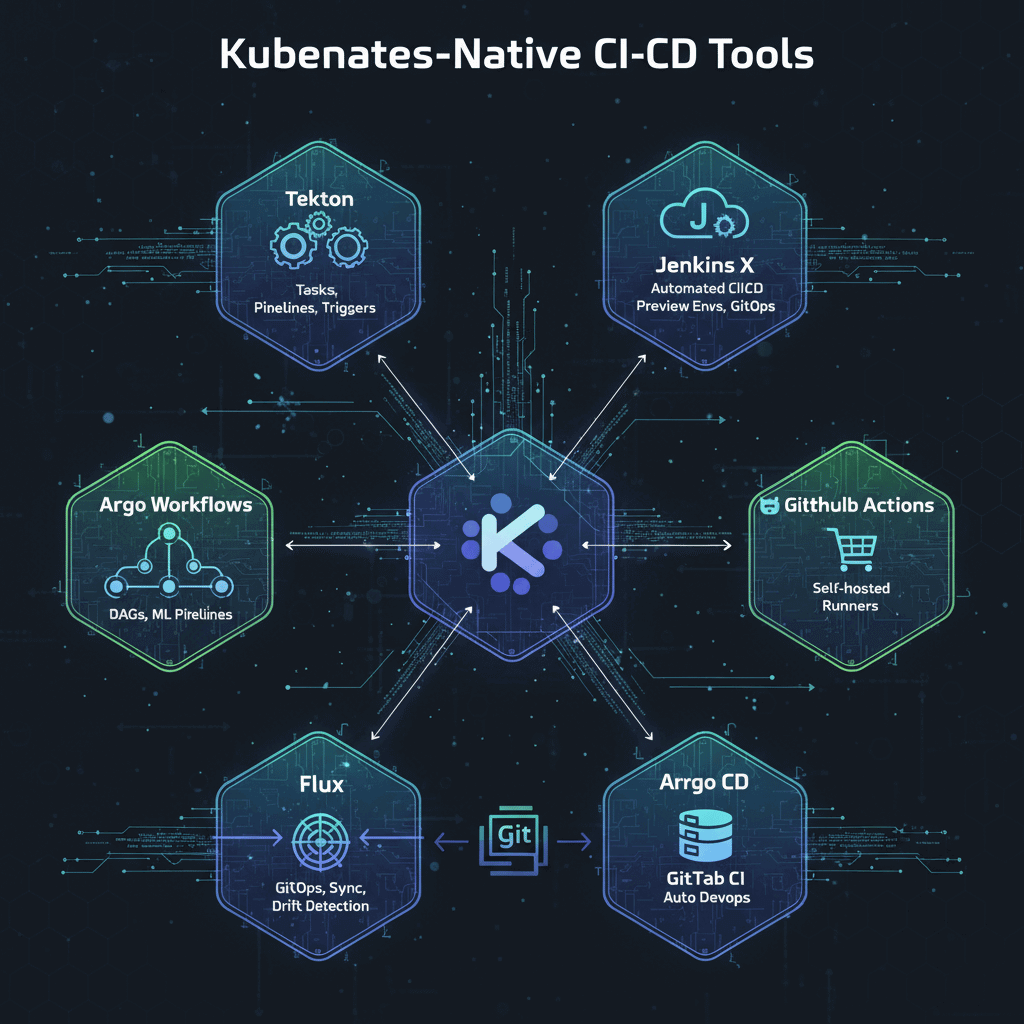
Tekton provides Kubernetes-native CI/CD primitives defined as Custom Resources. Tasks represent individual build steps. Pipelines compose tasks into workflows. Triggers automatically start pipelines in response to Git commits, pull requests, or webhooks. Tekton runs entirely on Kubernetes, leveraging native scalability and reliability.
Argo Workflows orchestrates complex workflows as directed acyclic graphs. Each workflow step runs in a separate container, enabling parallel execution and flexible dependency management. Argo Workflows excels at machine learning pipelines, data processing workflows, and multi-stage CI/CD processes requiring sophisticated orchestration.
Jenkins X extends Jenkins with cloud native capabilities including automated CI/CD for Kubernetes applications, preview environments for pull requests, and GitOps-based promotion across environments. Jenkins X provides opinionated workflows reducing configuration overhead while maintaining Jenkins flexibility.
GitHub Actions and GitLab CI offer hosted CI/CD services with Kubernetes integration. GitHub Actions provides marketplace workflows and self-hosted runners executing jobs in Kubernetes clusters. GitLab CI integrates tightly with GitLab repositories, offering Auto DevOps capabilities that automatically configure CI/CD based on detected application types.
Flux and Argo CD implement GitOps continuous delivery by continuously monitoring Git repositories and synchronizing Kubernetes cluster state. These tools enable declarative, Git-based deployment workflows with automatic drift detection and remediation.
GitOps Workflows
GitOps treats Git repositories as the single source of truth for declarative infrastructure and application definitions. Changes go through pull requests with peer review before merging. Automated controllers continuously reconcile cluster state with repository contents, ensuring actual state matches declared intent.
Benefits include complete audit trails through Git commit history, easy rollback by reverting commits, configuration drift detection highlighting manual changes, access control using Git branch protections, and multi-cluster deployment from centralized repositories.
Implementation requires separating application code repositories from deployment configuration repositories. Application repos contain source code and Dockerfiles. Deployment repos contain Kubernetes manifests, Helm values, and Kustomize overlays. CI pipelines update deployment repos with new image tags after successful builds. GitOps controllers detect changes and deploy automatically.
Argo CD architecture includes a server component providing API and web UI, application controller monitoring Git repositories, repo server managing Git credentials and manifest generation, and optional ApplicationSets enabling multi-cluster deployments. Argo CD continuously compares desired state in Git with actual cluster state, highlighting drift and enabling automated or manual synchronization.
Flux CD provides similar capabilities with modular architecture separating concerns. Source controller manages Git and Helm repositories. Kustomize controller reconciles Kustomize overlays. Helm controller manages Helm releases. Notification controller sends alerts to Slack, Microsoft Teams, or other systems.
Progressive Delivery Patterns
Progressive delivery gradually rolls out changes while monitoring metrics, automatically rolling back on errors. This approach reduces deployment risk compared to all-at-once releases.
Canary deployments route small traffic percentages to new versions while the majority continues using stable versions. Platform teams monitor error rates, latency, and business metrics. If canaries perform well, traffic gradually shifts to new versions. If errors spike, traffic automatically reverts to stable versions. Flagger automates canary deployments, integrating with service meshes like Istio and Linkerd for traffic management and metrics collection.
Blue-green deployments maintain two complete environments. Blue runs the current version while green deploys the new version. After validation, traffic switches atomically from blue to green. If issues arise, instant rollback switches traffic back to blue. This approach requires double infrastructure capacity but provides zero-downtime deployments with instant rollback.
Feature flags decouple deployment from release, allowing code deployment to production while features remain disabled. Teams gradually enable features for specific users or percentages, monitoring impact before full rollout. This enables testing in production with real user traffic while limiting blast radius.
Container Image Building
Multi-stage builds separate compilation from runtime, creating minimal production images. The first stage uses full build environments compiling code and installing dependencies. The second stage copies only runtime artifacts into minimal base images, reducing attack surface and image size. Multi-stage builds dramatically improve security and deployment speed.
Base image selection impacts security and maintainability. Use minimal images like Alpine Linux, distroless images containing only application and runtime dependencies, or scratch images for static binaries. Smaller images download faster, have fewer vulnerabilities, and reduce attack surface.
Image scanning identifies vulnerabilities in container images. Tools like Trivy, Grype, and Clair scan images during CI/CD builds, failing pipelines that exceed vulnerability thresholds. Regular rescanning detects newly discovered vulnerabilities in previously safe images, triggering rebuild and redeployment.
Image signing and verification ensure images come from trusted sources without tampering. Sigstore and Cosign provide cryptographic image signing integrated into CI/CD pipelines. Admission controllers verify signatures before allowing image deployment, preventing supply chain attacks.
Security Integration
Shift-left security embeds security scanning into early development phases. Static Application Security Testing analyzes source code for vulnerabilities. Software Composition Analysis identifies vulnerable dependencies. Container scanning validates images before deployment. Infrastructure as Code scanning checks Kubernetes manifests for misconfigurations.
Secret management prevents credentials in source code or CI/CD configurations. Integrate HashiCorp Vault, AWS Secrets Manager, or cloud provider secret stores. Pipelines retrieve secrets dynamically at runtime, injecting them as environment variables or mounted files. Secrets rotate automatically without pipeline updates.
Policy enforcement validates configurations against organizational standards. Open Policy Agent and Kyverno define policies preventing non-compliant deployments. Admission controllers automatically enforce policies during Kubernetes resource creation, blocking deployments violating security or compliance requirements.
Pipeline Best Practices
Keep pipelines fast through parallel test execution, incremental builds caching unchanged layers, and distributed test runners. Fast pipelines enable frequent commits with immediate feedback, accelerating development velocity.
Make pipelines reproducible using immutable build environments, pinned dependency versions, and hermetic builds preventing external dependencies. Reproducible pipelines enable confident troubleshooting and auditability.
Implement comprehensive testing including unit tests validating individual components, integration tests validating component interactions, end-to-end tests validating complete user workflows, and smoke tests validating production deployments.
Monitor pipeline health tracking build success rates, pipeline duration trends, test flakiness, and deployment frequency. Pipeline observability enables continuous improvement and early detection of degrading reliability.
Conclusion
Cloud native CI/CD pipelines transform software delivery by automating builds, tests, and deployments while integrating security throughout. GitOps workflows provide declarative, auditable deployment processes. Progressive delivery patterns minimize risk through gradual rollouts with automatic rollback. Kubernetes-native tools like Tekton, Argo CD, and Flux leverage platform capabilities for scalable, reliable pipelines.
Success requires fast feedback loops, comprehensive security integration, reproducible builds, and continuous pipeline improvement. Organizations mastering cloud native CI/CD deploy confidently and frequently, accelerating innovation while maintaining stability. The convergence of GitOps, progressive delivery, and Kubernetes-native tooling creates deployment workflows that are reliable, secure, and developer-friendly.