Securing Cloud-Native Applications
Protect containerized applications and Kubernetes with this comprehensive security guide. Covering zero trust, CI/CD pipelines, runtime threat detection, and compliance as code.
TL;DR
- Four Pillars of Defense: Cloud native security requires integrated controls across Cloud, Cluster, Container, and Code. Weakness at any layer compromises the entire stack, from infrastructure misconfigurations to application vulnerabilities.
- Shift Security Left, But Don't Stop There: Embed security in CI/CD pipelines with automated scanning (SAST, SCA, container scans) to catch issues early. However, this must be paired with runtime protection (behavioral monitoring, threat detection) to defend against zero-days and attacks that evade pre-deployment checks.
- Zero Trust is Foundational: Assume no entity is trustworthy by default. Implement service identities (SPIFFE), mutual TLS (mTLS) for encrypted, authenticated service-to-service communication, and enforce identity-based authorization policies, not just network rules.
- Automate for Compliance and Response: Treat compliance as code using policy engines like OPA. For runtime threats, enable automated responses (e.g., killing or isolating compromised containers) to contain breaches instantly, minimizing manual intervention.
Cloud native security protects containerized applications, Kubernetes clusters, and microservices across their entire lifecycle. As organizations deploy hundreds of times daily across distributed environments, traditional perimeter-based security fails.
This guide covers the four pillars of cloud native security, zero trust architectures, runtime protection, and compliance automation that security engineers need to protect modern applications without sacrificing velocity.
Four Pillars of Cloud-Native Security
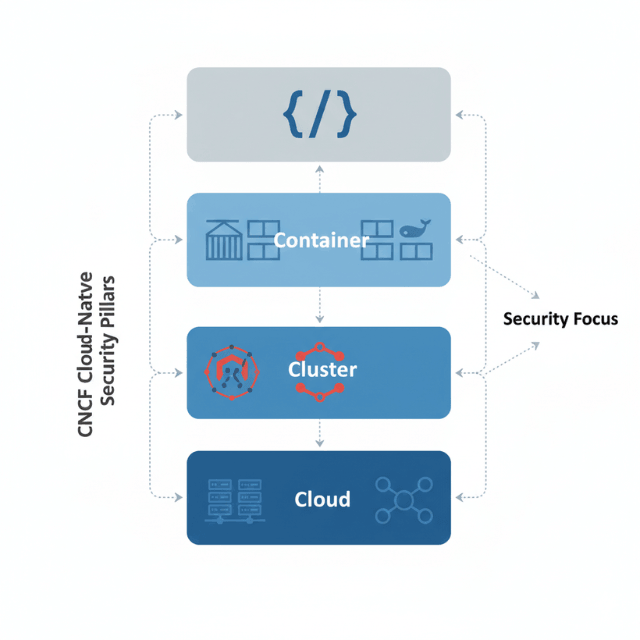
The CNCF defines four core security layers: Cloud, Cluster, Container, and Code. Each layer requires specific controls, and weakness at any level compromises the entire stack.
Cloud security encompasses underlying infrastructure including virtual networks, compute instances, storage, and identity management. Organizations must configure security groups properly, enable audit logging, encrypt data at rest and in transit, and implement least-privilege IAM policies. Cloud Security Posture Management tools continuously assess configurations against benchmarks.
Cluster security focuses on Kubernetes control planes and cluster configuration. Critical controls include API server authentication and authorization through strong mechanisms, RBAC policies following least privilege, network policies implementing microsegmentation, Pod Security Standards enforcing secure configurations, and admission controllers preventing policy violations.
Container security addresses image and runtime protection. Scan images for vulnerabilities before deployment, ensure images come from trusted registries, run containers as non-root users, restrict capabilities and privileges, and monitor runtime behavior for anomalies. Container security spans the entire lifecycle from build through production.
Code security encompasses application-level practices including secure coding standards, dependency management, secrets protection, and application authentication. Static analysis identifies vulnerabilities in source code, software composition analysis flags vulnerable dependencies, and dynamic testing validates running applications.
These pillars are interdependent. A code vulnerability can compromise containers. Misconfigured clusters expose secure containers. Cloud infrastructure weaknesses undermine cluster protections. Cloud native security requires integrated controls across all four layers.
Shift-Left Security in CI/CD Pipelines
Shift-left security embeds security practices into early development phases rather than treating security as final gatekeeping before production. This approach discovers vulnerabilities during development when they're cheapest to fix while providing immediate feedback to developers.
IDE integrations provide real-time feedback on insecure code patterns and vulnerable dependencies. Pre-commit hooks enforce security policies, preventing insecure code from entering version control. Developers catch issues immediately while context is fresh.
CI/CD pipeline integration makes every code commit trigger automated security scans. Static Application Security Testing analyzes source code for SQL injection, cross-site scripting, and hardcoded credentials.
Software Composition Analysis identifies vulnerable open-source dependencies. Container image scanning detects vulnerabilities, malware, and misconfigurations. Infrastructure as Code scanning validates security configurations in Terraform, Helm, and Kubernetes manifests.
Automated security gates enforce policies without manual reviews. Pipelines fail builds introducing critical vulnerabilities or violating organizational standards. Gates should be context-appropriate: development environments may allow lower severity issues, production requires strict enforcement.
Fast feedback loops enable quick remediation. Security scan results available within minutes of commits help developers fix issues immediately. Detailed remediation guidance reduces security team involvement. IDE integrations provide feedback even before code commits.
Security champions within development teams bridge security and development gaps. These trained developers interpret findings, champion secure practices, and provide development perspective to security discussions. This embedded expertise accelerates secure development.
Kubernetes Security Best Practices
Kubernetes security requires defense in depth across multiple layers. The platform's complexity introduces numerous potential misconfigurations that require systematic controls.
API server security forms the first defense line. Use strong authentication through client certificates, service account tokens, or OpenID Connect. Never expose the API server directly to public internet. Enable audit logging to track all API access.
RBAC governs authorization within clusters. Define roles specifying which operations are allowed on which resources. Bind roles to users and service accounts following least privilege. Avoid cluster-admin bindings across namespaces. Regularly audit RBAC configurations for excessive permissions.
Network policies provide microsegmentation within clusters. Kubernetes allows all pod-to-pod communication by default, facilitating lateral movement after compromise. Network policies implement zero trust by explicitly defining allowed communication paths. Start with deny-all policies and explicitly allow required traffic.
Pod Security Standards enforce security configurations at pod level. The Restricted profile enforces best practices: non-root containers, no privilege escalation, forbidden host namespaces, and limited capabilities. Enforce Baseline minimum and Restricted wherever possible.
Admission controllers intercept API requests before persistence, enforcing policies automatically. Tools like OPA Gatekeeper, Kyverno, and Kubewarden enable custom policies requiring specific labels, enforcing image signatures, blocking untrusted registries, and mandating resource limits.
Secrets management requires careful attention. Enable encryption at rest for secrets stored in etcd. Integrate external secrets management like HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault for stronger protection and centralized management across clusters.
Zero Trust Architecture
Zero trust assumes no user, device, or service is trustworthy by default. Every access request requires verification regardless of origin. Cloud native architectures make zero trust both critical and achievable through service identity and policy enforcement.
Service identity provides cryptographically verifiable identities for every workload. SPIFFE provides standardized identity issuance and verification. Service meshes implement SPIFFE through mutual TLS, where both client and server prove identities using certificates before communication.
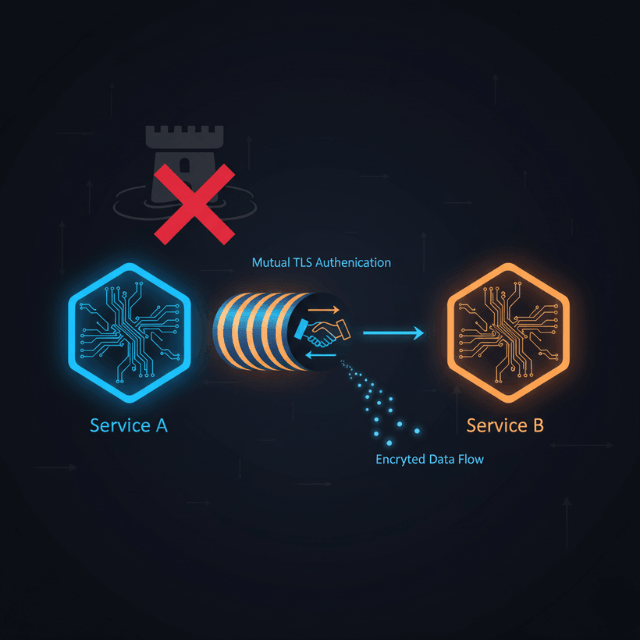
Mutual TLS encrypts service-to-service communication and provides bidirectional authentication. This prevents man-in-the-middle attacks and ensures services communicate only with authorized peers. Service meshes automate mTLS certificate issuance, rotation, and enforcement transparently to applications.
Authorization policies define which services can communicate based on verified identities rather than IP addresses. Policies might enforce that only the authentication service accesses user databases or only payment services access transaction processors. Identity-based authorization is more robust than network-layer controls.
Continuous verification evaluates trust based on behavior rather than initial authentication. Anomaly detection identifies unusual access patterns: services accessing unexpected resources, requests from unusual locations, or abnormal data access volumes. Continuous assessment enables rapid response to compromised identities.
API gateways serve as policy enforcement points in zero trust architectures. They authenticate requests, verify authorization, enforce rate limits, and log all access. Gateways provide centralized policy application across services while complementing distributed enforcement in service meshes.
Container and Image Security
Container security begins with the images serving as templates for running containers. Images composed of layers may contain outdated packages, known vulnerabilities, or malicious code requiring systematic controls.
Image scanning forms the security foundation. Automated scanners analyze image layers identifying vulnerable packages against CVE databases. Modern scanners also detect malware, hardcoded secrets, and configuration issues. Context-aware scanning prioritizes by considering whether vulnerable code is reachable and exploits exist.
Image provenance and signing ensure images come from trusted sources without tampering. Docker Content Trust and Sigstore enable cryptographic image signing. Configure registries and orchestrators to accept only signed images from approved publishers, preventing supply chain attacks.
Base image selection impacts security posture. Minimal images like Alpine Linux, distroless images, or scratch images reduce attack surface by including only essential packages. Distroless images contain only applications and runtime dependencies, eliminating package managers and shells attackers exploit.
Runtime security contexts enforce policies on running containers. Kubernetes security contexts control privileges, capabilities, and filesystem access. Run containers as non-root, make root filesystems read-only, and drop unnecessary Linux capabilities to reduce compromise impact.
Runtime monitoring detects anomalous container behavior establishing baselines and alerting on deviations: unexpected network connections, unusual process execution, or unauthorized file access. Runtime detection catches zero-day exploits and malicious activity that static scanning misses.
Image lifecycle management ensures images remain secure over time. Vulnerabilities are continuously discovered in previously safe packages. Regularly rescan deployed images, track which workloads run vulnerable images, and implement processes to rebuild and redeploy updated images automatically.
Runtime Security and Threat Detection
Runtime security detects and prevents threats in running applications, providing the last defense against zero-day vulnerabilities, sophisticated attacks, and malicious insiders.
Behavioral baselines establish normal container patterns using machine learning: which processes run, which network connections establish, which files are accessed, and which system calls execute. Deviations trigger alerts. This catches attacks exploiting application vulnerabilities to execute arbitrary code.
Process monitoring detects malicious activity like cryptocurrency miners, backdoors, or lateral movement tools. When containers suddenly spawn shells and execute suspicious commands, runtime security raises alarms. This is particularly effective against code execution exploits.
Network monitoring detects suspicious communication: connections to known malicious IPs, unusual data exfiltration, or communication to services workloads shouldn't access. East-west traffic monitoring between services catches lateral movement attempts evading perimeter defenses.
File integrity monitoring detects unauthorized filesystem changes. While containers should be immutable, compromised containers often have modified files for persistence. Detecting modifications enables rapid incident response.
Automated response contains threats without manual intervention. When malicious behavior is detected, systems automatically kill offending containers, isolate them from networks, create forensic snapshots, and spin up clean replacements. This limits damage while maintaining availability.
Compliance in Cloud Native Environments
Compliance in cloud native environments requires mapping traditional regulatory frameworks to ephemeral infrastructure. Continuous compliance replaces periodic audits as infrastructure changes constantly.
Compliance as code expresses requirements as machine-readable policies automatically enforced. Open Policy Agent, Kyverno, and cloud-specific tools enable policies preventing non-compliant configurations. This prevents violations from reaching production rather than remediating after deployment.
Audit logging satisfies accountability requirements. Capture Kubernetes API access, container execution, data access, authentication events, and configuration changes. Store logs immutably in centralized systems preventing tampering with long-term retention.
Data residency poses challenges in multi-cloud environments. Ensure sensitive data remains in specific jurisdictions as regulations require. Use Kubernetes topology awareness, node selectors, and pod affinity for residency controls, carefully configured and continuously verified.
Encryption requirements apply to data at rest and in transit. Encrypt container registry contents, persistent volumes, secrets in etcd, and all network traffic between services. Document encryption mechanisms, key management practices, and certificate lifecycle management for auditors.
Vulnerability management demonstrates security patch management. Identify vulnerabilities, assess risk, and remediate critical issues within defined timeframes. Container image scanning, runtime vulnerability detection, and patch tracking provide required evidence.
Conclusion
Cloud native security fundamentally evolves application protection from perimeter-based defenses to integrated, automated security throughout development and deployment. The dynamic, distributed nature of cloud native architectures demands security approaches that are equally dynamic and automated.
Successful implementation balances multiple priorities: securing the entire stack from cloud through code, shifting security left while maintaining runtime detection, adopting zero trust while preserving development velocity, and managing compliance through automation. The journey is iterative, starting with foundational capabilities and progressively adding sophistication.
Culture matters as much as technology. Security teams must enable developers rather than block them. Development teams must own security within their domains. Platform teams must build security into internal platforms. When security becomes everyone's responsibility with seamless tool integration, organizations achieve DevSecOps promises: accelerating deployment velocity while improving security outcomes.
Cloud native security done well becomes a competitive advantage through reduced breach risk, accelerated time to market, and improved customer trust. Organizations mastering cloud native security deploy faster, respond to threats quicker, and meet compliance requirements more efficiently than competitors struggling with legacy approaches.
FAQs
What's the biggest mistake teams make when starting with cloud native security?
Focusing on only one layer, typically containers, while neglecting cluster and cloud configuration.
A common pitfall is scanning container images for vulnerabilities (good!) but leaving the Kubernetes API server exposed or using overly permissive RBAC roles, which completely undermines image security.
If we "shift left" and scan everything in CI/CD, do we still need runtime security?
Absolutely. Shifting left reduces vulnerabilities reaching production, but it cannot catch everything.
You need runtime security to detect zero-day exploits, configuration drift, compromised credentials, and malicious insiders—threats that don't exist as code vulnerabilities at build time.
How does zero trust apply to communication between my microservices?
It means you don't automatically trust traffic just because it's inside your cluster. Implement a service mesh to assign every service a strong identity (SPIFFE) and encrypt all traffic with mutual TLS (mTLS) .
Then, enforce policies that allow communication only between identified services that need to talk (e.g., only the "payment" service can talk to the "transaction" database).
Summarize this post with:
Ready to put this into production?
Our engineers have deployed these architectures across 100+ client engagements — from AWS migrations to Kubernetes clusters to AI infrastructure. We turn complex cloud challenges into measurable outcomes.